Iranian-Affiliated Hackers Are Targeting US Infrastructure
Default credentials and open ports are all it takes.
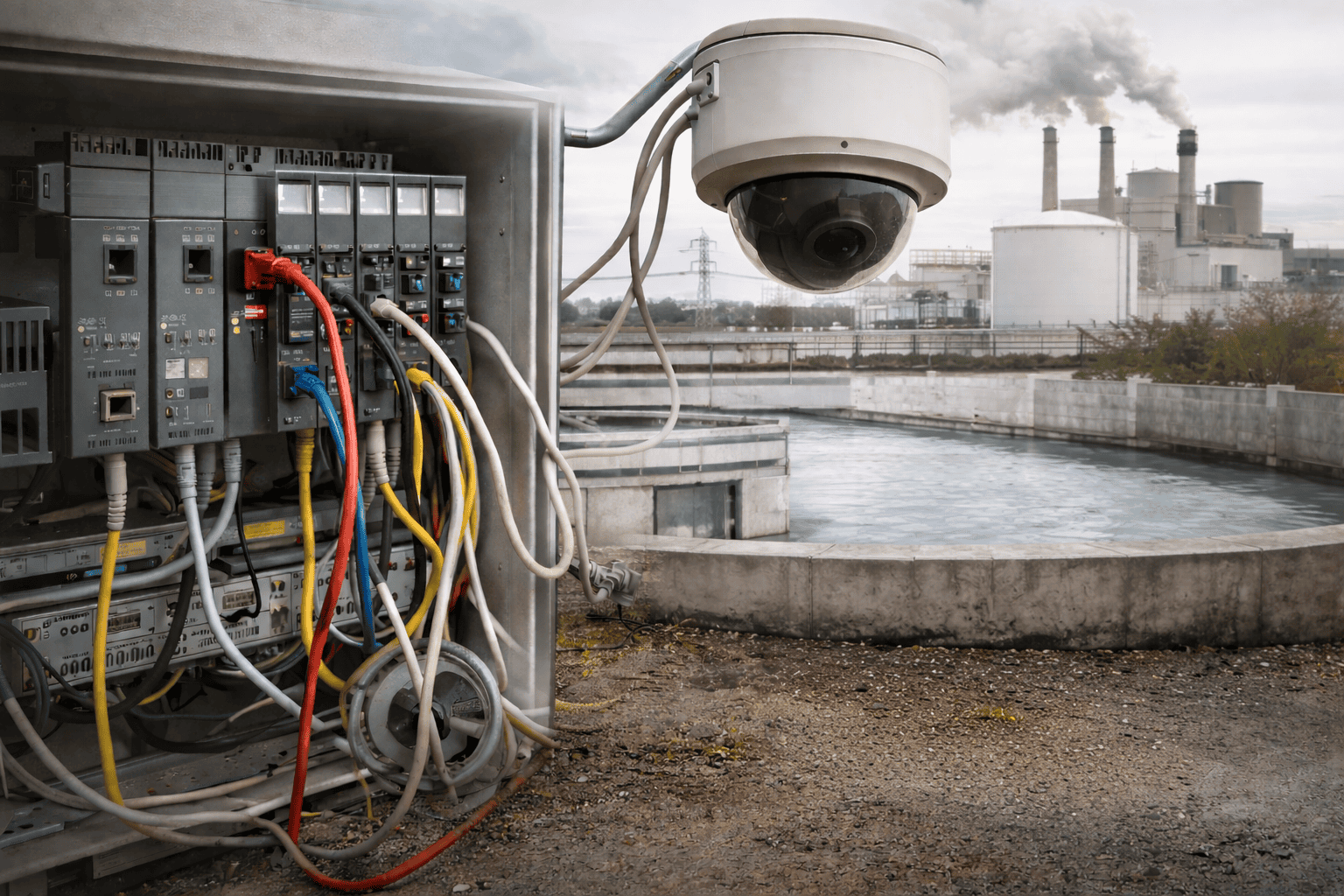
Iranian-affiliated hackers breached a Pennsylvania water utility in 2023. They’re back, and the attack scope is wider. On April 7, 2026, six federal agencies published a joint cybersecurity advisory warning that Iranian-affiliated threat actors are exploiting internet-connected programmable logic controllers (PLCs) at US energy and water providers. This hacking method works on most any business network. Not just utilities.
Security cameras, printers, point-of-sale systems, and smart thermostats on your network right now potentially share the same fundamental weakness that breached US critical infrastructure: they’re internet-connected, poorly authenticated, and no one’s watching them.
What the Advisory Recommends
Every one of those devices ships with a factory-default login and sits on a network with no segmentation, no hardening, and no one watching. The same automated scanning tools that nation-state actors use on critical infrastructure can find yours, too. The same attack methods that hit enterprises hit small businesses, too, and they work more often because small businesses are likely to be more vulnerable.
These four actions are recommended for all businesses, not just utilities:
Most Small Business Networks Aren’t Ready for This
Iranian-affiliated APT groups get the headline. The real story is simpler.
Most small businesses run a consumer-grade firewall with factory settings. No segmentation. No log review. No firmware updates. No one watching. That setup doesn’t survive an amateur hacker, let alone a nation-state operation. Ask Green River, Wyoming how fast ransomware shuts down an organization that thought it was too small to matter.
Managed IT closes the gap. A managed firewall is configured for your environment, updated as threats change, and monitored around the clock. Endpoint protection accounts for every device. When a federal advisory drops, a managed IT provider doesn’t forward the article to you. They’ve already reviewed it, checked your exposure, and acted.
That’s the difference between having IT and having managed IT.
Managed IT. Managed Security. One Call.
SC Network Solutions provides managed firewall services, endpoint security, and 24/7 network monitoring for businesses across Southern Utah and Northern Arizona.
Three Things to Do Before End of Week
Find out if your network is exposed. Schedule Your Free Risk Assessment Now